7 Types of Hacker Motivations

Hackers are not created equal, nor do they have the same purpose. Some hackers are paid to scrutinize security systems, find loopholes, fix weaknesses, and ultimately protect organizations and people. Others exploit those same gaps for profit, power, or disruption. What separates hackers isn’t just skill level or tactics; it’s intent.
The purpose behind an attack changes everything about how hackers shape their tactics and how the hacking process unfolds: who is targeted, which methods and tools are used, how patient the attacker is, and the kind of damage they want to cause.
The primary motivations behind these cyberattacks fall into several categories, from financial gain to recognition, and sometimes even coercion. Each driver creates different risk scenarios for your digital life, from your home banking sessions to your workplace communications. Understanding a hacker’s motivations will enable you to better protect yourself and recognize potential threats in both your personal and professional life.
In this article, we’ll look at the main types of hackers you might encounter, the core motivations and mindset that drive these cyberattacks, and finally, how you can protect yourself against these attacks.
Good and bad hackers
From its beginnings as an intellectual exploration in universities, hacking was driven by curiosity, learning, and the thrill of solving complex problems. Today, it has become industrialized with organized criminal groups and state-sponsored actors entering the scene.
Modern hacking has seen the emergence of advanced persistent threats and nation-state campaigns targeting critical infrastructure and combining traditional techniques with artificial intelligence. To better understand the types of hackers, here is a window into what they do and why:
White hat hackers
These are the good guys, typically computer security experts who specialize in penetration testing and other methodologies to ensure that a company’s information systems are secure. These IT security professionals rely on a constantly evolving arsenal of technology to battle hackers.
Black hat hackers
These are the bad guys, who are typically referred to as just plain hackers. The term is often used specifically for hackers who break into networks or computers, or create computer viruses. Unfortunately, black hat hackers continue to technologically outpace white hats, often finding the path of least resistance, whether due to human error or laziness, or with a new type of attack. Hacking purists often use the term “crackers” to refer to black hat hackers, whose motivation is generally to get paid.
Script kiddies
This is a derogatory term for black hat hackers who use borrowed programs to attack networks and deface websites in an attempt to make names for themselves. Script kiddies, sometimes called script kitties, might be beginners, but don’t be fooled by their newbie status. With the right tools and right targets, they can wreak as much havoc as a seasoned hacker.
Hacktivists
Some hacker activists are motivated by politics or religion, while others aim to expose wrongdoing or exact revenge. Activists typically target government agencies, public services, and organizations involved in controversial issues related to defense, elections, wars, finance, or social movements. They also attack high-profile individuals, such as executives, public figures, journalists, and activists.
State-sponsored hackers
State-sponsored hackers have limitless time and funding to target civilians, corporations, other governments, or even prominent citizens connected to a larger objective. Their motivations are driven by their government’s strategic goals: gathering intelligence, stealing sensitive research or intellectual property, influencing public perception, or disrupting critical infrastructure. Because they are playing a long game, state-sponsored hackers are stealthy and persistent, quietly embedding themselves in systems, mapping networks, and waiting for the right moment to act.
Spy hackers
Corporations hire hackers to infiltrate their competitors and steal trade secrets, including product designs, source code, pricing plans, customer lists, legal documents, and merger or acquisition strategies. They may hack from the outside or gain employment in order to act as a mole, impersonating recruiters, partners, or vendors to get insiders to share access. They also take advantage of weak internal controls, such as excessive permissions, unsecured file-sharing links, or poor offboarding practices. Spy hackers may use similar tactics as hacktivists or state-sponsored espionage on a smaller scale: stealthy entry, careful privilege escalation, and long-term persistence to avoid triggering alarms. The stolen data is often not leaked publicly but delivered directly to the client and used behind the scenes.
Cyber terrorists
These hackers, generally motivated by religious or political beliefs, attempt to create terror, chaos, and real-world harm by disrupting critical infrastructures such as power grids, water systems, transportation networks, hospitals, emergency services, and government operations. They combine cyber operations with propaganda campaigns and physical attacks on the systems people rely on to live safely to create turmoil far beyond the screen.
Understand hackers’ motivations
Cybercriminals aren’t just faceless entities; they’re driven by specific goals that shape their tactics and targets. Understanding their motivations empowers you to recognize potential threats and better protect yourself, your family, and colleagues.
Financial gain
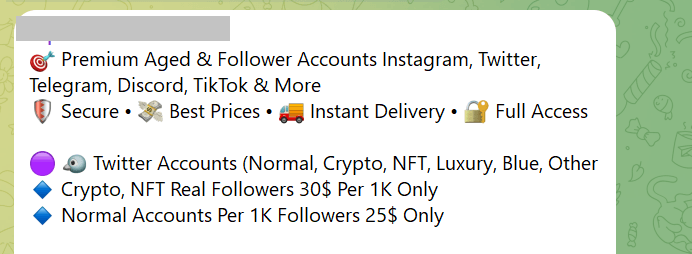
Money remains the most common motivator. These profit-driven attacks directly impact your personal finances through methods such as ransomware, credit card fraud, and identity theft. In your home, financially motivated hackers target your banking apps, shopping accounts, and personal devices to steal payment information or hold your data hostage. In the workplace, they focus on payroll systems, customer databases, and business banking credentials.
Ideological motivations
Ideologically driven hackers, called hacktivists, pursue political or social causes through cyber means. These attacks can disrupt services that you rely on daily, from public utilities to private organizations that provide essential services or take public stances on divisive issues. Your best defense involves staying informed about potential disruptions and maintaining backup communication methods for essential services.
Curiosity and learning
Many hackers begin their journey with genuine curiosity about how systems work. They might probe your home network, test website security, or experiment with app vulnerabilities, not necessarily for malicious purposes, but their activities can still expose your data or disrupt services. In professional environments, these individuals might target systems or databases simply to see if they can gain access.
Recognition and reputation building
Some hackers seek fame, respect within hacker communities, or professional advancement rather than immediate financial benefit. They often target high-profile individuals, popular websites, or well-known companies to maximize the visibility for their exploits. If you have a significant social media following, your accounts could become targets for these attacks. They might also focus on defacing company or government websites, or leaking non-sensitive but embarrassing information.
State and corporate intelligence
Nation-state and corporate espionage are some of the most sophisticated threats in cyberspace, making it a top national security concern for both government and private sector. These operations compromise daily services and infrastructure such as internet service providers, email platforms, or cloud storage services to gather intelligence such as intellectual property, customer lists, or strategic planning documents.
Coercion and extortion
Some hackers use cyber capabilities to intimidate or coerce victims into specific actions. In the FBI’s Internet Crime Complaint Center report for 2024, extortion was the 2nd top cybercrime by number of complaints, demonstrating the growing prevalence of coercion-based attacks. Coercion might involve compromising personal photos, social media accounts, or private communications to demand payment or behavioral changes. Workplace coercion could target executives with embarrassing information or threaten to leak sensitive business data unless demands are met.
The intersection of motivations
Many real-world attacks combine multiple motivations—a financially driven criminal might also seek recognition within hacker communities, or an ideological hacker might generate revenue through ransomware. The contrast between ethical hacker motivations and malicious ones often lies in the permission, legality, and intent. Understanding why people become hackers helps you recognize that not all hacking activity is inherently malicious, although all unauthorized access ultimately poses risks to your security and privacy.
The psychology behind cyberattacks
Understanding the psychology behind cyberattacks gives you a powerful advantage in protecting yourself. When you know what drives hackers, you can better spot their tactics and stay one step ahead.
High reward, low risk
Many hackers operate with the goal of achieving high reward for perceived low risk. This risk-reward imbalance motivates attackers because they can potentially access valuable personal or financial information while remaining physically distant from their victims. This means hackers often target easy opportunities, such as when you click on suspicious links or download questionable attachments, to gain access with minimal effort. For instance, a hacker would rather send 10,000 phishing emails hoping for a few bites than attempt one complex, risky attack.
Exploiting normal human responses
Hackers exploit well-known psychological shortcuts your brain takes. They understand that you’re more likely to trust familiar-looking emails, act quickly under pressure, or follow authority figures without question. These aren’t weaknesses, these are normal human responses that attackers deliberately manipulate. For example, urgent messages claiming your account will be closed create an artificial time pressure, making you more likely to click without thinking.
The power of group dynamics
Many successful cyberattacks leverage the human tendency to follow what others are doing. Hackers create fake social media profiles, forge customer reviews, or impersonate colleagues to make their requests seem legitimate and widely accepted. In ransomware attacks targeting businesses, criminals often research company hierarchies and communication styles to make their demands appear to come from trusted sources within the organization.
The gamification of cybercrime
Modern hacking has elements that make it feel like a game to perpetrators. Some online forums award points for successful attacks, creating competition and recognition among criminals. This helps explain why some hackers target individuals rather than large corporations, as every successful phishing attempt becomes a score, and why attacks continue to evolve.
Common hacking methods
Hackers don’t all use the same tricks, but most successful attacks rely on a familiar toolkit of methods that exploit common technical gaps and human habits. Recognizing these common techniques will help you avoid danger earlier on.
- Phishing and smishing. These attacks trick you into revealing sensitive information through fraudulent emails or text messages, respectively known as phishing and smishing. Modern attackers increasingly use AI-generated content and sophisticated social engineering techniques that make these messages appear more legitimate than ever before.
- Credential stuffing. Cybercriminals use automated tools to test stolen username and password combinations across multiple websites, exploiting the fact that many people reuse passwords. This attack method has become more efficient with attackers leveraging large-scale data breaches and improved automation tools.
- Multi-factor authentication (MFA) fatigue. Attackers repeatedly send multi-factor authentication requests until overwhelmed, frustrated, and confused users approve one. This technique has gained prominence as more organizations adopt MFA, with attackers finding ways to exploit user behavior around security notifications.
- Malvertising. Malicious advertisements on legitimate websites can install malware or redirect you to harmful sites without requiring any clicks. Recent trends show attackers using sophisticated techniques to bypass ad network security filters.
- Remote desktop attacks. Hackers exploit weak or default passwords on remote desktop services to gain unauthorized access to systems, particularly targeting businesses with remote work setups. The rise of hybrid work environments since 2023 has made this attack vector increasingly attractive to cybercriminals. Disable remote desktop services when not needed and use VPNs with strong authentication for legitimate remote access.
- USB baiting. Attackers leave infected USB devices in public places, hoping curious individuals will plug them into their computers, automatically installing malware. Modern USB attacks can execute within seconds of being connected, making them particularly dangerous in today’s fast-paced work environment.
- Unsecured Wi-Fi networks. Unsecured public Wi-Fi and home networks create opportunities for hackers to gain access to your devices or intercept your sensitive information, such as passwords, emails, and banking details. Sometimes, cybercriminals create fake Wi-Fi hotspots with legitimate-sounding names to trick users into connecting.
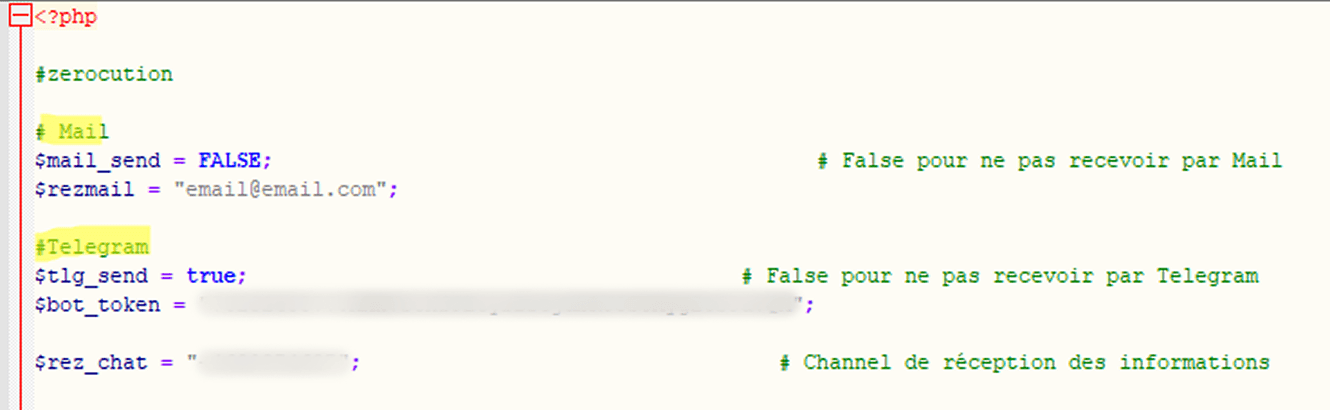
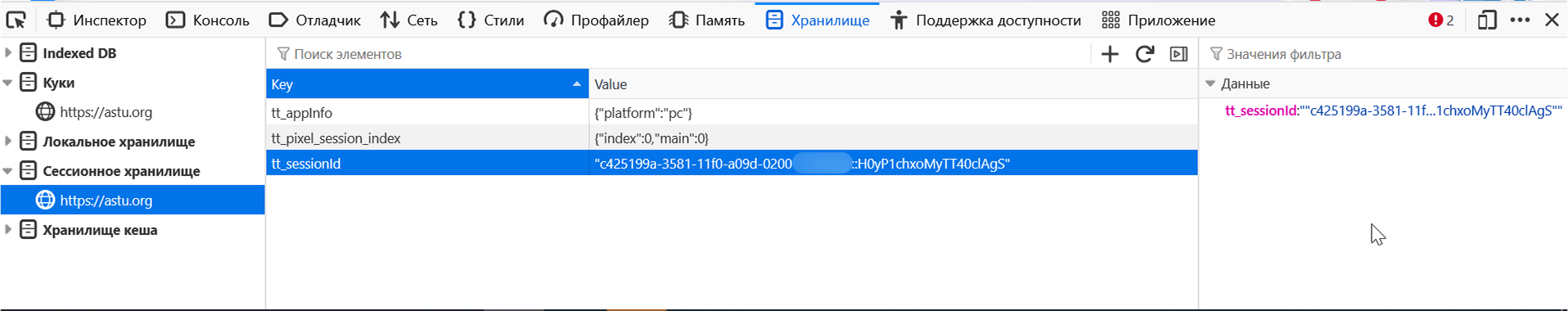
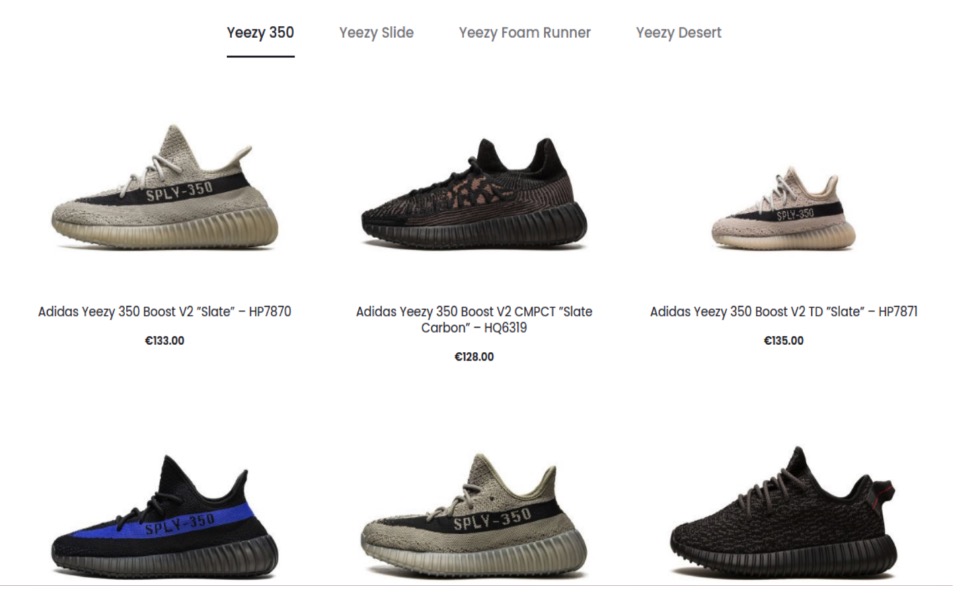
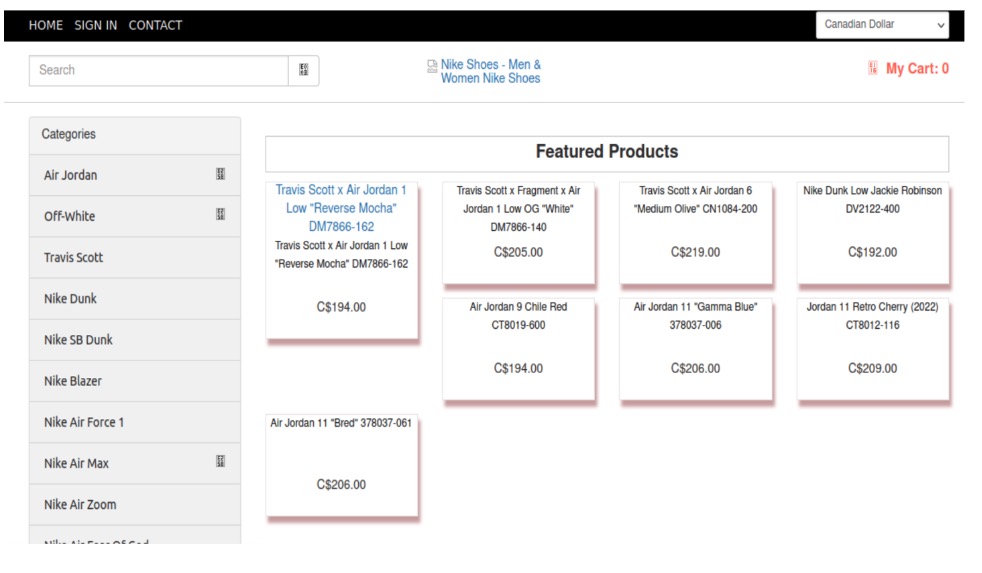
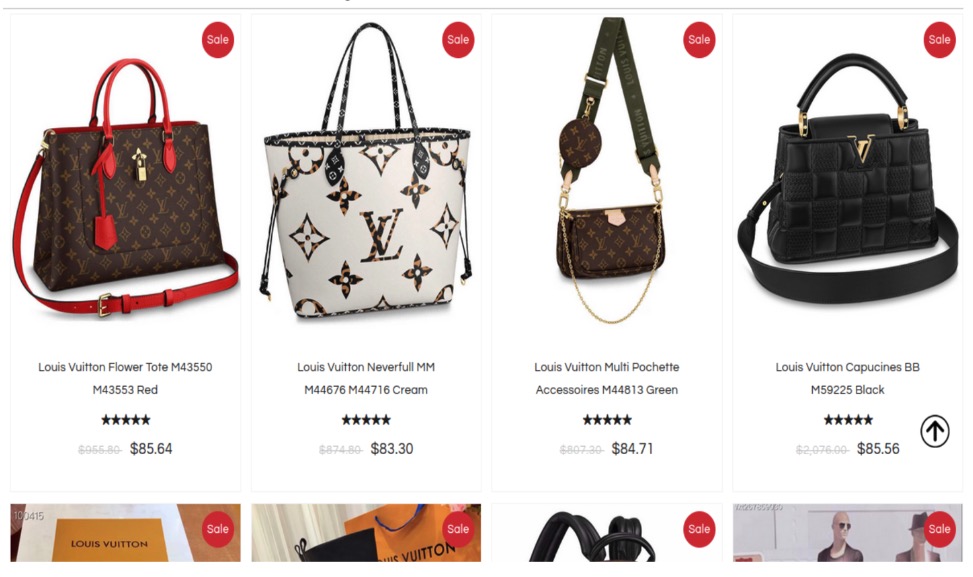
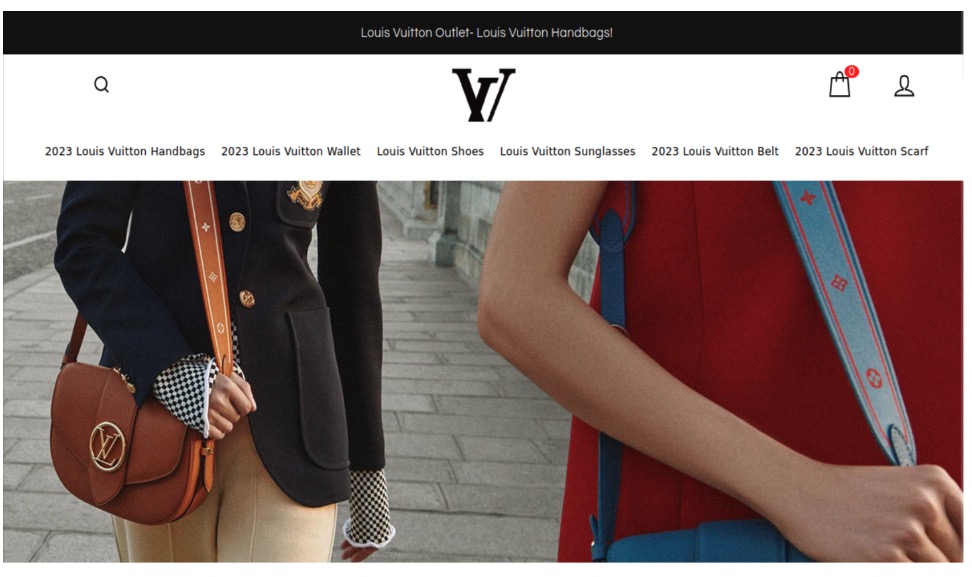
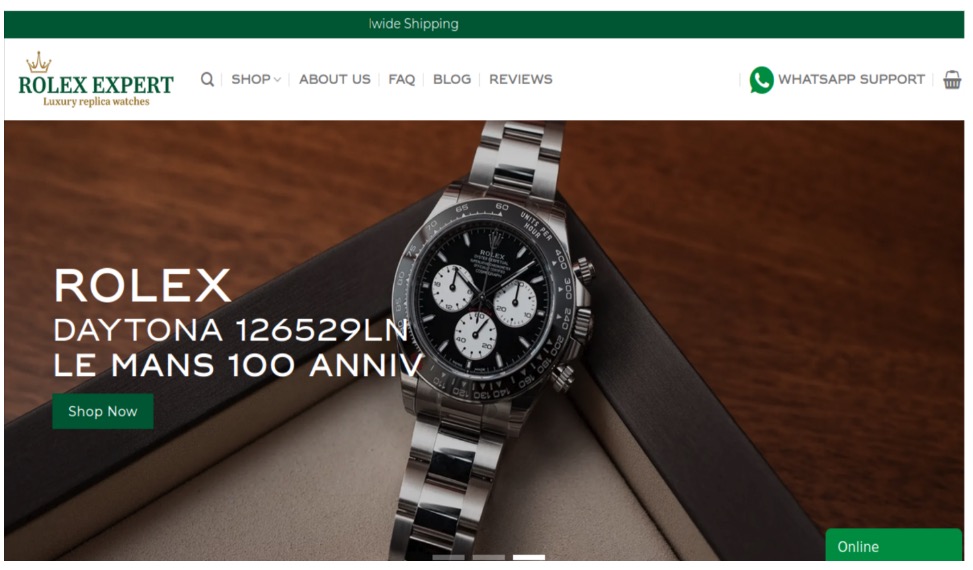
- Unsafe downloads. Hackers disguise malicious software as legitimate programs, games, documents, or updates to trick users into installing them. These malicious downloads may come from infected email attachments, fake or pirated software, or even compromised websites. Once installed, the malware can steal your information, lock your files for ransom, or give hackers access to your computer.
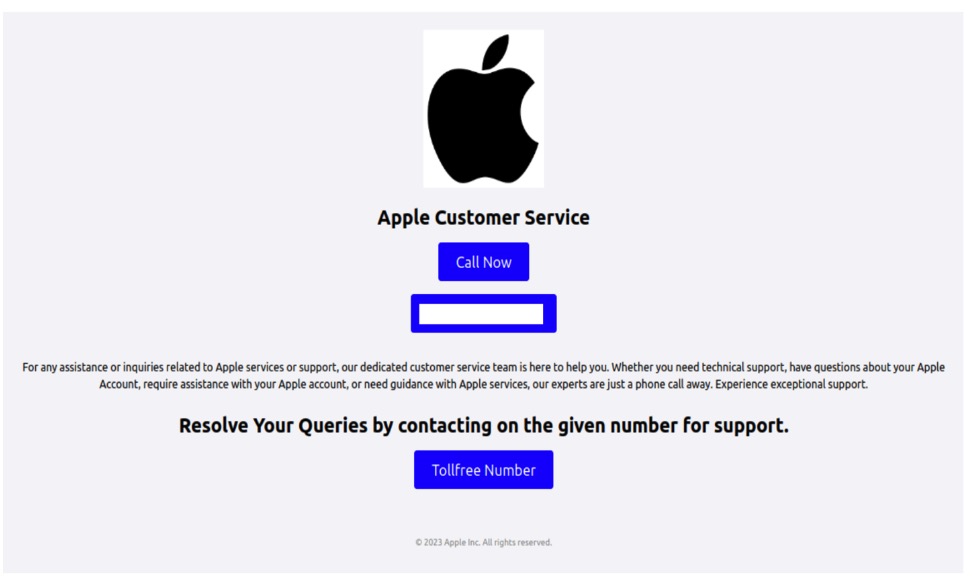
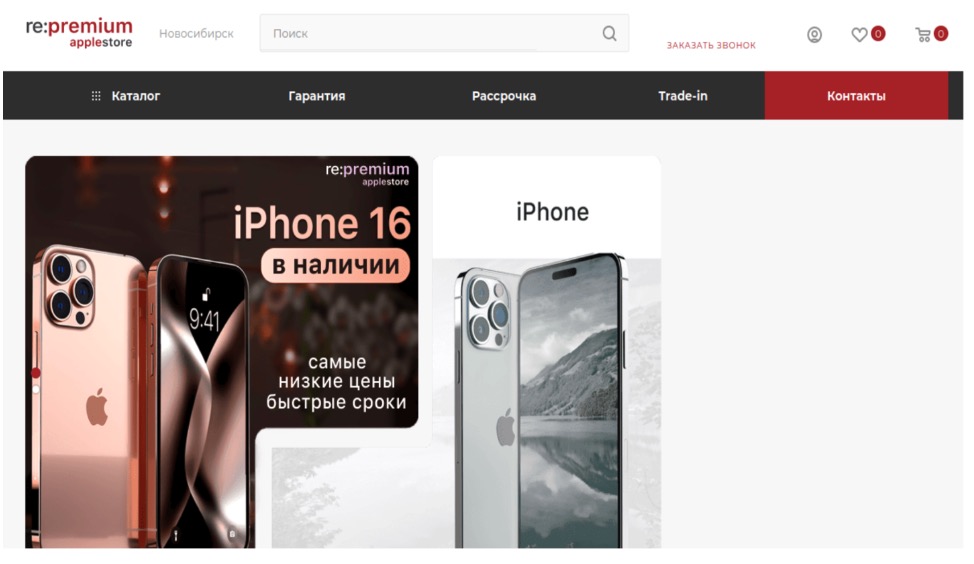
- Tech support scams. Tech support scams rely on social engineering rather than technical exploits, where scammers typically contact you by phone and insist your computer has been infected or compromised. They create urgency and fear to convince you to install remote access software that gives them complete control of your computer. Once they have access, they can steal personal information, install malware, or hold your files hostage.
- Outdated software. Running outdated software creates security vulnerabilities that hackers actively leverage. When software developers discover security vulnerabilities, they release patches to fix these problems. If you don’t install these updates promptly, your system remains vulnerable to attacks. Hackers maintain databases of unpatched systems and use automated tools to find and exploit them.
Defensive tips to protect yourself from hack attacks
Your strongest defense against hacking combines technical safeguards, security awareness, and some consistent habits that shut down the most common paths attackers use. Here’s how to put those defenses in place and make your digital life a much harder target.
- Install comprehensive security software. The Cybersecurity and Infrastructure Security Agency recommends a layered security approach to prevent multiple types of threats simultaneously. Choose a reputable security suite that offers real-time protection, anti-malware scanning, and web browsing safety features.
- Enable MFA everywhere. Add an extra security layer to all your important accounts: email, banking, social media, and work platforms. Only approve MFA requests that you initiated yourself, and report any unexpected authentication prompts to your IT team or service provider immediately.
- Use a password manager. Create complex, unique passwords using a trusted password manager for every account you own. The National Institute of Standards and Technology recommends passwords that are at least 12 characters long and completely unique across all your accounts to prevent credential stuffing attacks.
- Keep all software updated. Enable automatic updates for your operating system, apps, and security software, as many successful cyberattacks exploit known weaknesses that could have been prevented with timely updates.
- Secure your internet connections. Avoid using public Wi-Fi for sensitive activities, and use a reputable VPN when you must connect to untrusted networks. Unsecured public networks make it easy for attackers to intercept your data and credentials.
- Implement the 3-2-1 backup strategy. Regular, tested backups are your best defense against ransomware and data loss incidents. Keep three copies of important data—on your device, on an external drive, and in secure cloud storage.
- Develop scam-spotting skills. Scammers continuously adapt their tactics to current events, so staying informed about the latest schemes and learning to recognize phishing emails, suspicious links, and social engineering tactics will help you stay one step ahead.
- Practice good digital hygiene. Regularly review your account permissions, remove unused apps, and monitor your financial statements for unauthorized activity to lessen your exposure to identity theft and privacy breaches.
- Monitor your accounts regularly. Check bank statements, credit reports, and account activity monthly. Set up account alerts for unusual activity when available.
- Limit personal information sharing. Only provide the necessary information to companies or service providers to reduce your digital footprint. In addition, review privacy settings and avoid oversharing on social media as scammers and hackers regularly prowl these platforms.
Final thoughts
Now that you understand hackers’ motivations and psychological drivers, you can flip the script and turn it to your advantage. Instead of being the target, become the informed defender who recognizes manipulation tactics and responds thoughtfully rather than reactively. This knowledge empowers you to spot potential threats earlier, choose stronger protective measures, and navigate the digital world with greater confidence.
When someone pressures you to act immediately, that’s your cue to slow down and verify the request. Question familiar-looking messages, even if they look official. Check the sender’s address and contact the company through official channels. Trust your instincts and investigate before acting. Stay curious and keep learning from reputable cybersecurity resources that publish current research and threat intelligence. Share these tips with your family members and friends, especially those who might be less technologically savvy.
McAfee+ includes proactive identity surveillance to monitor subscribers’ credit and personal information, as well as access to live fraud resolution agents who can help subscribers work through the process of resolving identity theft issues.
The post 7 Types of Hacker Motivations appeared first on McAfee Blog.




 trustmark, indicating that the site has been scanned and verified as secure by a trusted third party. This security seal indicates that the site will help protect you from
trustmark, indicating that the site has been scanned and verified as secure by a trusted third party. This security seal indicates that the site will help protect you from